Preemptive Cybersecurity - The Future of Digital Defense
What Is Preemptive Cybersecurity?
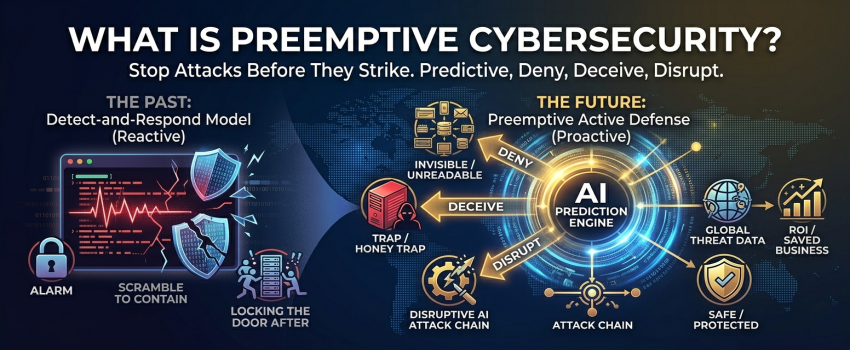
Most organisations today still run on a detect-and-respond model — they wait for an alarm to go off, then scramble to contain the damage. That model made sense a decade ago. Today, it is like locking the door after the thief has already left.
Preemptive cybersecurity flips the entire equation. Instead of waiting for something to go wrong, it uses artificial intelligence, machine learning, and predictive analysis to anticipate attacks before they are launched. The goal is simple: make your systems so unpredictable, so invisible, and so well-fortified that an attacker never gets a foothold in the first place.
Why does this matter right now?
Cyber threats in 2026 are no longer generic. Attackers use AI to craft personalised, tailored attacks against specific organisations — studying your systems, your employees, and your weak points before striking. Defending against that level of sophistication requires an equally intelligent, proactive response.
The Three Pillars: Deny, Deceive, Disrupt
Every preemptive cybersecurity strategy is built on three core actions. Think of them as your organisation's three lines of active defence:
Deny: Your systems are made invisible or unreadable to anyone who should not be there. Attackers cannot exploit what they cannot find. Even if someone slips inside a network, they encounter locked doors at every turn.
Deceive: Fake servers and decoy environments are deployed inside your network. When an attacker stumbles into one, they believe they have found a real target — but they have actually walked into a trap. Their every move is silently recorded and used to strengthen real defences.
Disrupt: Using intelligence gathered from global threat data, the system identifies attack patterns early and cuts them off. The attacker never reaches the stage of doing damage because the chain was broken at its very first link.
In-Depth Articles
The Arms Race You Cannot Afford to Ignore
AI is being used on both sides of the cyber battleground — and right now, the attackers are moving faster.
Modern cyber threats are no longer written once and sent to a thousand targets. They now adapt in real time — changing their behaviour to slide past security tools that were never designed to face a moving target. This is not a distant future concern; it is happening today. Organisations that rely purely on signature-based or rule-based defences are discovering, often the hard way, that their tools cannot keep pace. The answer is not simply adding more tools — it is changing the strategy entirely. Preemptive approaches use the same AI power to get ahead of the attacker rather than chase behind them.
Honey Traps: The Clever Way Security Teams Turn the Tables
What if the best way to understand your enemy was to let them think they had already won?
Deception technology places convincing fake environments inside a real network — ghost servers, dummy files, phantom user accounts. When an intruder interacts with any of these, an alert fires instantly. Security teams learn exactly what the attacker is looking for, how they operate, and what tools they are using — all without the attacker knowing they have been caught. This intelligence is not just useful for the immediate incident; it feeds directly into improving future defences. It is one of the most elegant ideas in modern security: let curiosity become the enemy's greatest weakness.
Reading the Room: Spotting Trouble Before It Starts
The most dangerous moment in any attack is the quiet period before anything visibly goes wrong.
Preemptive systems constantly analyse patterns of behaviour across every account and device on a network. Normal activity has a rhythm — login times, file access, communication patterns. When something subtly shifts, even before any rule is broken, the system takes notice. Credentials may be quietly rotated. A suspicious session may be isolated. An analyst may receive a heads-up. All of this happens automatically, without waiting for a human to spot the warning signs. It is the digital equivalent of a good security guard who notices something is off before anything has actually happened.
How Banks Are Building Walls That Cannot Be Mapped
Financial institutions have always been prime targets. Now they are leading the way in making themselves impossible to attack.
Banks and fintech companies handle enormous volumes of sensitive transactions every single day, making them perennial targets for sophisticated attacks. Many have now moved beyond simply monitoring for suspicious activity — they are actively restructuring their internal networks so that no outsider can map what lies inside. Using a technique called Automated Moving Target Defence, internal systems shift and rotate continuously, meaning that any intelligence an attacker gathers quickly becomes outdated. Combine this with AI-driven intent monitoring and rapid credential rotation, and the result is a financial institution that is genuinely difficult to target effectively.
Knowing What Is Coming Before It Arrives
The best time to prepare for an attack is long before it is launched.
Preemptive security systems do not work in isolation. They gather intelligence continuously from a wide range of sources — tracking emerging threat patterns, new attack techniques being discussed in underground communities, and global incident data from organisations around the world. This intelligence is fed into a central engine that correlates patterns and flags likely attack paths. Security teams can then reinforce those areas before an attack materializes. Rather than being reactive, they are operating on a form of strategic foresight — positioning their defences not where attacks have been, but where they are most likely to come next.
Protecting the Systems That People's Lives Depend On
Hospitals and healthcare networks face a unique challenge: they cannot afford a single moment of disruption.
Healthcare is one of the most targeted sectors in the world, and the stakes could not be higher. Patient records, medical devices, diagnostic systems — a disruption to any of these can have real-world consequences for patient safety. That reality has pushed healthcare organisations to adopt preemptive security strategies faster than almost any other sector. Moving attack surfaces, strict access controls, and continuous behavioural monitoring have become standard practice in leading hospitals and health networks. The goal is not just to recover quickly from an incident — it is to ensure an incident never happens at all.
Expert Perspective
“Preemptive cybersecurity is about acting before attackers strike — using AI-powered operations, programmatic denial, and deception. This is a world where prediction is protection.”
— Tori Paulman, VP Analyst, Gartner 2026
“AI-driven threats are polymorphic and adaptive, changing in real time to evade known defences. Simply put, they now move too fast for manual or purely detection-based systems to handle.”
— International Banker, February 2026
How We Got Here: A Timeline
2024 - The Tipping Point
AI-powered attacks begin outpacing traditional detection tools. Less than 5% of security spending is proactive. The industry starts recognising that reactive defences have a fundamental ceiling.
2025 - A New Strategic Direction
Gartner names Preemptive Cybersecurity a Top 10 Strategic Technology Trend. Financial services, healthcare, and government sectors begin deploying deception technology and predictive intelligence at scale.
2026 - Mainstream Momentum
Preemptive solutions are projected to account for 35% of all cybersecurity spending. AI threats are now personalised, autonomous, and highly adaptive. Prevention-first strategies move from best practice to business requirement.
2028 - A Shifted Industry
The majority of enterprise security teams measure success not by how fast they respond to attacks, but by how many attacks never reached their systems at all.
2030 - The New Standard
Half of all global cybersecurity spending is projected to be preemptive in nature. Prediction-based defence becomes the baseline expectation for organisations of every size.
Key Takeaways
- Preemptive cybersecurity stops attacks before they reach your systems, rather than responding after damage has occurred.
- The three core strategies — Deny, Deceive, and Disrupt — form the foundation of all preemptive defence frameworks.
- Artificial intelligence enables systems to detect unusual behavioural patterns and act on them automatically, without waiting for human intervention.
- Deception technology turns attacker curiosity into an intelligence advantage for defenders.
- Financial services and healthcare are leading early adoption, driven by the high value of their assets and the critical nature of their operations.
- Gartner forecasts that preemptive solutions will account for 50% of all cybersecurity spending by 2030.
- Organisations that act now will be far better positioned than those who wait for the technology to become standard.
The question is no longer whether to adopt preemptive cybersecurity.
It is whether you will adopt it before or after your next incident.
Related to this
Let's Discuss Your Project











